StormWall operates scrubbing centers across the USA, Europe, Southeast Asia, and the Middle East, delivering over 8 Tbps of combined filtering capacity. Our infrastructure handles massive volumes of malicious traffic every day, giving us a clear picture of what is happening across the global DDoS threat landscape.
In this report, we cover the main attack patterns, which industries were hit the hardest, and how attacks were distributed across different countries during Q1 2026.
You might also want to read our global 2025 DDoS report.

Q1 2026 Main Trends
DDoS activity jumped sharply in the first quarter of 2026. The ongoing conflict in the Middle East fueled a wave of hacktivist campaigns around the world, reversing the shift toward profit-driven attacks that we saw in the second half of 2025.
DDoS Attacks Up 168%
DDoS attacks grew by 168% year-over-year in Q1 2026 — a massive jump compared to the 80% growth recorded in Q4 2025. This is the fastest rate of growth StormWall has recorded in years.
The biggest driver was the escalation of the conflict in the Middle East. In late February 2026, the US and Israel launched joint airstrikes against Iran, which triggered a wave of retaliatory hacktivist campaigns across the globe. Within just 72 hours of the initial strikes, more than 150 hacktivist DDoS attacks were recorded, targeting over 100 organizations across 16 countries.
If you have been following our previous reports, you may recall that in Q4 2025 the threat landscape shifted from hacktivism toward profit-driven attacks. That trend has now reversed.
Politically motivated groups — many of them pro-Iranian and pro-Palestinian — returned in force in Q1 2026, and hacktivism once again became the primary driver of DDoS activity.
Their targets also changed. Government agencies, financial institutions, airports, telecom providers, and energy infrastructure across the Middle East, Europe, and other regions became primary targets. Hacktivists are once again focusing on critical infrastructure.
At the same time, the attacks themselves became more powerful. This combination of higher volume and increased intensity placed serious pressure on organizations that were not prepared for sustained, large-scale DDoS campaigns.
Multi-Vector Attacks Up 128%
Multi-vector DDoS attacks — where attackers use several different methods at the same time — became 128% more common in Q1 2026 compared to the same period last year.
Multi-vector attacks are more difficult to defend against because each vector targets a different layer of infrastructure. Mitigating one type of attack does not stop the others, which means protection systems must handle multiple threats simultaneously.
The growth of multi-vector attacks also puts additional pressure on traditional DDoS defenses. Systems designed to handle only one type of traffic can struggle when attackers launch simultaneous attacks from multiple directions. This is particularly critical for organizations in the telecommunications and financial sectors, where even a few minutes of downtime can have significant operational and financial consequences.
Attack Share Breakdown by Industry
Now let’s look at how DDoS attacks were spread across all industries in Q1 2026:
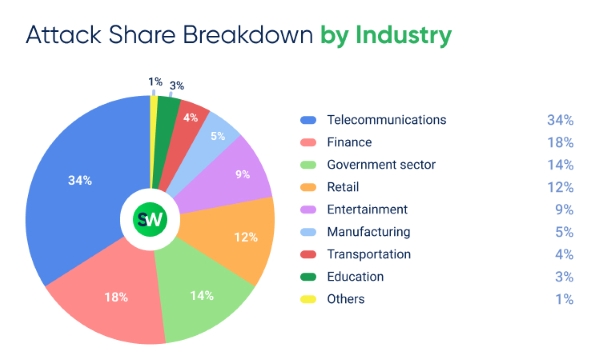
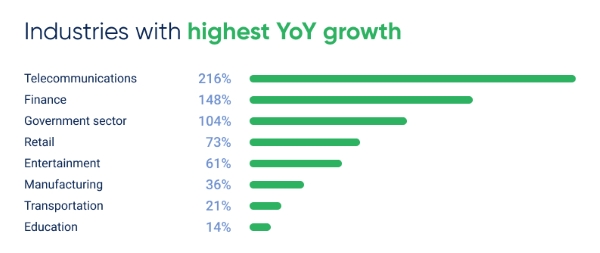
Industries with highest YoY growth in DDoS attacks in Q1 2026:
Here is how the relative share of attacks shifted from Q4 2025 to Q1 2026:
- The share of attacks on telecommunications companies increased from 26% in Q4 to 34% in Q1
- In contrast, financial services saw a decline from 22% to 18%, despite a 148% year-over-year increase in total attack volume
- The government sector, meanwhile, rebounded from 10% to 14%, reversing its earlier decline
- Retail’s share dropped from 14% to 12% as politically motivated attacks overtook financially driven ones
- Entertainment also saw a decrease, from 12% to 9%
This represents a reversal of the trend observed in Q3–Q4 2025. At that time, profit-driven attackers focused on industries where extortion is most effective — retail, finance, and entertainment.
In Q1 2026, as hacktivist activity increased, the focus shifted back to high-profile, politically and strategically important targets: telecom companies, financial institutions, and government infrastructure.
Relative Risk of DDoS
Which sectors are most likely to be targeted, and which are relatively safe? The table below shows the relative likelihood of being attacked by industry:
| Industry | Chance of Being Attacked |
| Telecommunications | ~1 in 3 |
| Finance | ~1 in 5.5 |
| Government Sector | ~1 in 7 |
| Retail | ~1 in 8.5 |
| Entertainment | ~1 in 11 |
| Manufacturing | ~1 in 20 |
| Transportation | ~1 in 25 |
| Education | ~1 in 33 |
| Others | ~1 in 100 |
Note: this is a relative risk based on the global distribution of attacks. Actual risk depends on factors such as exposure surface, security posture, and whether an organization is actively targeted.
Top 3 Most Attacked Sectors: A Closer Look
Let’s take a closer look at the three industries that were hit the hardest.
1. Telecommunications
Telecommunications was by far the most targeted industry in Q1 2026. Hacktivist groups deliberately targeted telecom providers to cause maximum disruption — taking down a telecom provider affects not just one company, but every business and user relying on its network.
Among the known targets were an Israeli telecom provider attacked as part of a coordinated 72-hour campaign across 16 countries, as well as a Tel Aviv-based communications company targeted by a North African hacktivist group.
TCP flood attacks remained the primary vector, but there was also a sharp increase in multi-vector campaigns targeting telecom infrastructure from multiple angles simultaneously.
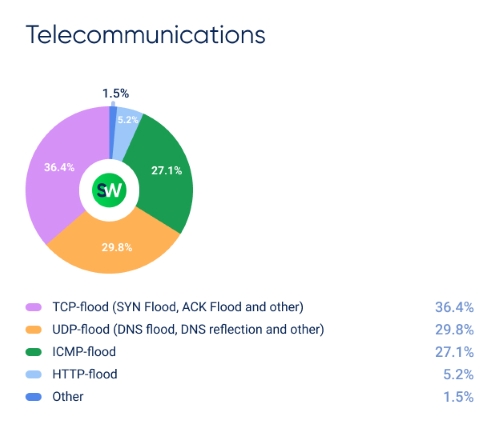
Attackers also continued to use legacy and less common protocol floods, including Teeworlds, RIPv1, and VxWorks floods. This trend first appeared in Q3 2025 and continued to grow through Q1 2026.
2. Finance
The share of attacks targeting the financial sector decreased from 22% in Q3 2025 to 18%, but the total volume of attacks increased significantly. This indicates that attacks did not decrease — rather, other industries experienced faster growth.
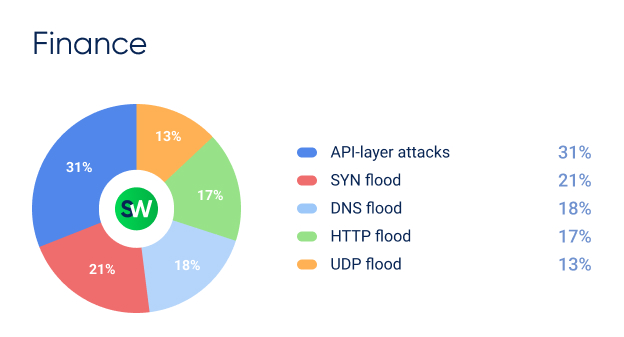
Multiple banks across the Middle East were targeted by DDoS attacks in Q1, while financial institutions in the US increased monitoring efforts. The industry body SIFMA confirmed heightened alert levels, and US intelligence warned of potential Iran-aligned DDoS attacks on financial networks.
More than 71% of attacks on financial institutions involved multiple vectors, and 44% used three or more — both figures increased significantly compared to Q4 2025.
3. Government Sector
The share of attacks on government institutions increased by 4% quarter-over-quarter, reversing the decline observed in the second half of 2025.
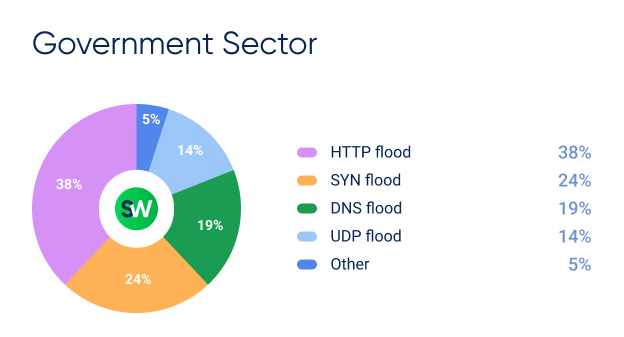
In Kuwait, attackers targeted the Armed Forces website, the Ministry of Defense, and the main government portal. In Qatar, a separate campaign targeted the government portal, the Ministry of Foreign Affairs, the Ministry of Education, and the Ministry of the Interior.
DDoS Attacks Breakdown by Country
Let’s look at how DDoS attacks were distributed by country in Q1 2026:
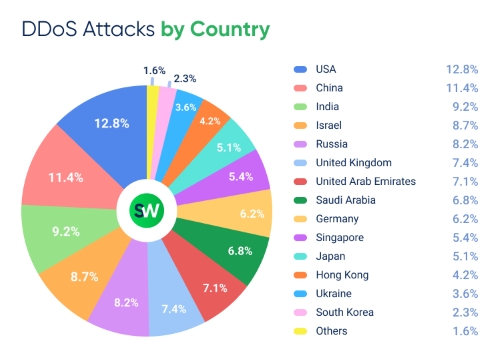
The top three most targeted countries remained the same: the USA (12.8%), China (11.4%), and India (9.2%). Together, they accounted for 33.4% of global DDoS traffic, slightly down from 37% in the previous quarter.
One of the most notable developments this quarter was Israel’s return to the top five. After dropping out of the top ten in Q4 2025, it rose to 8.7% due to the escalation of the Middle East conflict and the resulting hacktivist campaigns.
At the same time, Russia’s share decreased from 9.6% in Q3 to 8.2%, while Japan remained stable at 5.1%. France and Belgium, which appeared in the Q4 top rankings, were replaced by the UAE, Saudi Arabia, and Hong Kong — all locations closely connected to ongoing developments in the Middle East.
Notable shifts from Q4 2025 to Q1 2026 include:
- Israel (+): outside top 10 → 8.7%
- UAE (+): 4.3% → 7.1%
- Saudi Arabia (+): 6.2% → 6.8%
- Singapore (+): 3.7% → 5.4%
- Hong Kong (+): 2.3% → 4.2%
- USA (–): 14.2% → 12.8%
- China (–): 12.6% → 11.4%
- Russia (–): 9.6% → 8.2%
- France (–): 7.3% → dropped from top 14
- Belgium (–): 2.6% → dropped from top 14
Wrapping Up
Modern DDoS campaigns tend to follow a recurring pattern. During periods of geopolitical tension, government-backed or politically motivated attackers take center stage. These actors are often highly skilled, well-equipped, and capable of launching large-scale operations.
As they develop new tools and techniques, these capabilities eventually propagate beyond their original creators. The NSA’s EternalBlue exploit is one well-known example, but this pattern continues across the entire ecosystem — from state-developed tools to DDoS-as-a-service platforms that now allow anyone to launch attacks at a relatively small cost.
”Looking ahead, it is reasonable to expect record-breaking DDoS campaigns in the coming months — both in terms of scale and duration. Organizations must ensure their protection systems are prepared to handle worst-case scenarios across all regions, with elevated risk in areas experiencing ongoing geopolitical tensions,” says Ramil Khantimirov, Co-founder and CEO of StormWall.

DDoS Protection for Websites
- Activate protection in 10 minutes
- 24/7 technical support




















