At the end of 2023, we at StormWall were taking a deep dive into the data from this year. We’ve been closely examining the DDoS attacks that targeted our clients. In our latest report, we highlight how these trends have shifted since 2022. If you want to learn about the state of DDoS attacks in 2022, read our 2022 Year in Review report.
We’ve based our analysis on data from our global network of scrubbing centers. These centers, positioned in key locations around the world, can handle massive amounts of data—up to 3500 Gbit/s at their busiest. It’s this data that gives us a clear view of the current state of DDoS threats worldwide.
Main takeaways
The year 2023 was exceptionally busy for cyber threats, with a notable change in attack strategies. We saw an increase in multi-vector attacks, attacks targeting the DNS protocol, and the use of smoke-screening and VM-based botnets capable of launching large-scale attacks.
The overall firepower of DDoS threat actors has increased significantly. A clear example is the recent attack on Google Cloud in October, which was over seven times more powerful than any previous, reaching 398 million RPS. This escalation in attack power has had a major impact on businesses globally.
Compared to 2022, the total number of DDoS attacks worldwide in 2023 went up by 63%. Geopolitical factors were a major driver of this increase. The influence of these factors grew throughout the year and was especially pronounced in the fourth quarter, aligning with the start of the conflict between Israel and Palestine in October.
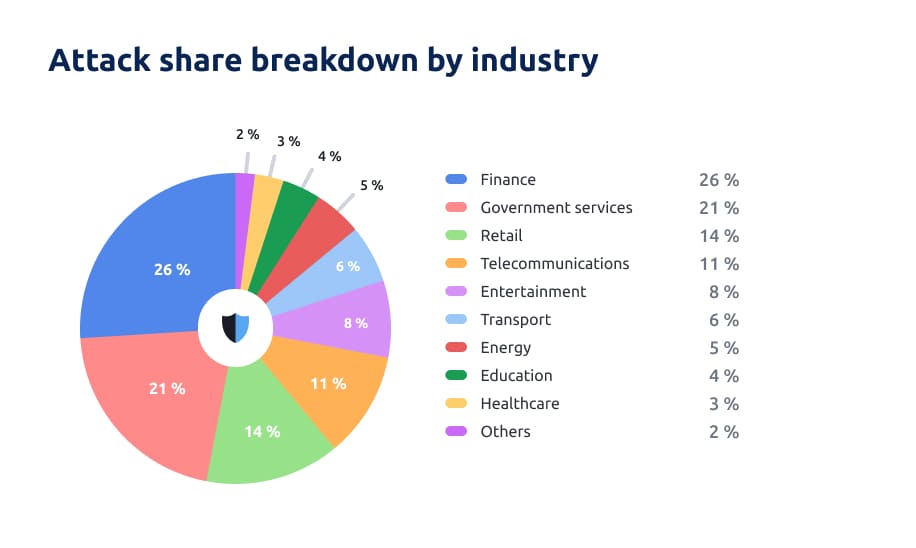
In terms of industries affected, finance was the most targeted, accounting for 26% of the attacks. This was followed by government services at 21% and retail at 14%.
DDoS attacks: overview of the global trends
– Geopolitics is the main driver behind the majority of DDoS attacks. Geopolitics was a key driver behind the increase of DDoS attacks. We’re saw attacks increased across countries like the USA, Russia, Ukraine, Israel, Germany, France, Poland, and the UAE, mainly because of increased activities of state-backed cyber gangs and APTs
– Multi-vector attacks are on the rise. Compared to 2022, we’ve seen a 108% jump in multi-vector attacks. A big part of this increase comes from more attacks being launched by state-sponsored groups in 2023. These groups are not only more advanced technically, but they also have access to sophisticated tools.
– Smokescreening is widely deployed. We’ve also seen a 54% rise in smokescreening. This technique involves using DDoS attacks to distract from other malicious activities, such as data exfiltration or network penetration.
– The biggest attack against our clients peaked at 1.4 terabits. In 2023, the biggest attack StormWall blocked peaked at 1.4 terabits per second. To put it in perspective, that’s about as much data as a small country’s entire daily internet traffic.
– Botnets evolved to become extremely destructive. Botnets played a big role in DDoS attacks, with 43% involving them. Initially, IoT botnets were common, but as the year progressed, they were overtaken by more powerful VM botnets running on cloud computing platforms.
– Geographical reach of DDoS attacks is expanding. There’s been a noticeable uptick in DDoS attacks in the APAC and MENA regions. Particularly in MENA, where DDoS activity surged by 45% in the last quarter of 2023. This spike is mainly due to Russian companies moving there to dodge sanctions or tap into new markets, attracting the attention of both state-backed and profit-driven hackers.
– Hackers are beginning to target DNS more and more. DNS attacks also saw an increase in 2023, going up by 28% compared to 2022. These remain among the most effective tools in a hacker’s arsenal.
Here are the main trends to highlight this quarter:
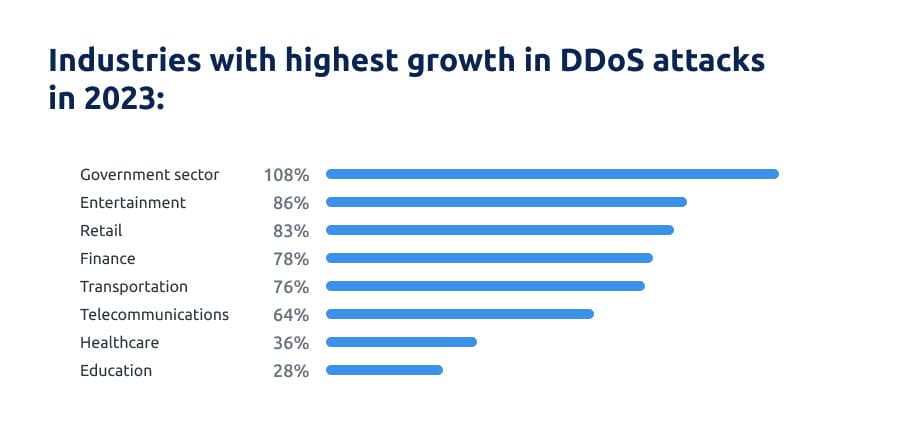
- For the first time in our reports, the government sector has become the second most targeted vertical, with attacks skyrocketing by 108%. It’s now the fastest-growing sector for cyber attacks this year.
- A closer look at the industry-wise breakdown reveals a shift towards targeting critical infrastructure. Sectors like transport control, energy grids, and government services should be especially vigilant.
- There’s also a surge in attacks on the retail and entertainment sectors, particularly in the APAC and MENA regions. These areas are rapidly digitizing, which makes them attractive to hackers looking to take advantage of developing security setups.
Finance
In 2023, the financial industry bore the brunt of DDoS attacks, with 26% of all attacks targeting this sector. Although there was a 78% increase in attacks compared to the previous year, it’s relatively modest next to the 12-fold growth from 2021 to 2022
This year also highlighted a direct connection between DDoS attacks and ongoing conflicts like those in Israel-Palestine and Russia-Ukraine. Israeli banks, in particular, faced attacks from threat actors in Indonesia, India, Bangladesh, and Russia’s Killnet.
In the Middle East’s finance sector, we observed volumetric attacks peaking at 135Gbps, and web DDoS attacks hitting 2 million requests per second. These attacks not only disrupted payment processing during the conflict but also served as a distraction for concurrent malware or ransomware hacks.
Government services
In 2023, attacks on government services made up 21% of incidents globally, almost catching up to the financial sector. This is the first time we’ve seen this sector experience so much DDoS activity. The government sector also leads in terms of YoY growth, with a staggering 108% increase in attacks. To compare, just last year, attacks on government services weren’t statistically significant enough to enter our list of top industries.
The use of cyberwarfare in the Russia-Ukraine conflict has, in a way, popularized attacks on government systems. They’re now a widespread issue, particularly active in the Middle East due to the Israel-Palestine conflict, and the impact is also felt across the EU.
The state-sponsored groups behind these attacks are highly organized and employ sophisticated DDoS tactics. These include multi-vector attacks, DNS amplification, TCP direct-path, and application layer attacks.
Retail
DDoS attacks in the retail industry made up 14% of incidents, with a year-over-year growth of 83%. In the APAC region in particular, 40% of attacks were directed at Ecommerce, marking a 170% increase YoY regionally.
Focus on ecommerce was most pronounced in India and China, where the retail subvertical made up over 50% of the attacks. This rise is linked to the increased use of loyalty and rewards programs in online shopping. Also, as tourism gets back to pre-pandemic levels, online platforms for hotel and flight bookings are facing more attacks.
The MENA region also saw a rise in DDoS attacks aimed at the ecommerce sector. Economic sanctions have led many Russian companies to move from EU and US markets to these regions, which have experienced an economic uplift. This has attracted cybercriminals, who are either politically motivated or target Russian companies to exploit companies for extortion.
Telecommunications
The telecom sector experienced an 11% share of DDoS attacks, with a 64% year-on-year increase. Attackers frequently employed the ‘Carpet Bombing’ and ‘Bits and Pieces’ method, which involves dispersing small packets of junk traffic across a wide range of IP addresses. We also saw a wide use of DNS water-torture attacks within the telecom industry.
In 2022, StormWall identified the telecommunications sector as the second most targeted industry for DDoS attacks. In 2023, its growth rate in attacks slowed down compared to other industries, but it remained high, especially in the APAC region. This trend was partly due to the shift of many broadband gaming users to 5G fixed wireless access, as providers expanded their networks. This expansion caught the attention of hackers.
Entertainment
In the entertainment sector, DDoS attacks accounted for 8% of the total, with an 86% surge from 2022, which is the second highest growth rate of all verticals. Gaming servers and betting services were the primary targets. Attackers often utilized cloud platforms to create powerful botnets, overloading gaming and betting servers with HTTP protocol traffic.
We noticed a frequent use of DDoS botnets that amalgamate various malware types, all managed by a single command and control server. These mixed botnets employed a layered attack approach, where each sub-group targets a different network component, leading to a substantial volumetric impact.
The strategy’s main goal was to overwhelm game servers, rendering games unplayable. This disruption often resulted in a rapid decrease in player numbers, which attackers then exploited to demand ransom payments.
Transport
The transport sector faced 6% of the cyber attacks, showing a 76% increase year-over-year.
State-backed hackers mainly targeted this industry. In the first half of the year, most attacks focused on European Union countries. Noteworthy incidents included DDoS attacks by Anonymous Sudan against French organizations, hitting major players like airports, Air France, Transavia, and FlyingBlue. The rail sector wasn’t spared either, with Paris’s RATP and the national rail service SNCF also being attacked. Additionally, both Ukraine and Russia witnessed DDoS campaigns targeting their transport networks, particularly railways, as these systems were critical for moving troops to frontlines.
Scandinavian airlines and airports also became targets of state-sponsored hackers, including Anonymous Sudan. These attackers demanded ransoms as high as $10 million, leveraging DDoS attacks to apply pressure.
Other noteworthy industries
- Energy sector. The energy sector accounted for 5% of the total cyber attacks. A significant incident occurred in Denmark during the first half of the year, targeting the nation’s key energy infrastructure. Hackers employed the Mirai botnet, impacting more than 20 state-level energy providers. Similarly, in Israel, the Gaza-based group Storm-1133 targeted Israeli entities in defense, energy, and telecommunications sectors, marking an uptick in such attacks in early 2023.
- Education. The education sector experienced 4% of all cyber attacks, showing the lowest growth rate at 28%. These attacks primarily targeted higher education institutions in the European Union and Russia and were linked to hacktivism. The timing of most incidents coincided with major exams and the start of new academic terms, with the main goal being to disrupt enrollment processes. Interestingly, for-profit hackers showed less activity in this industry, than hacktivists.
- Healthcare. The healthcare industry was the target of 3% of global DDoS attacks, witnessing a 36% rise in attacks compared to the previous year. This increase was particularly noticeable in the APAC region, with Singapore’s public health institutions being heavily affected. In many cases, these DDoS attacks served as a diversion, masking the simultaneous data theft of personal patient records.
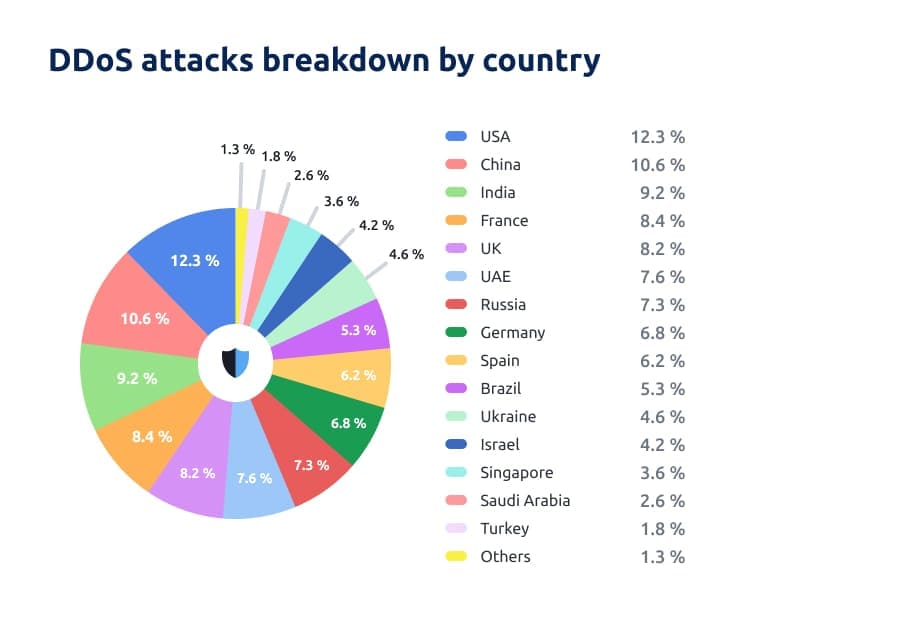
The USA continues to lead in terms of DDoS attack frequency, accounting for 12% of the attacks globally. China follows closely with 10.6%, and India is next with 9.6%. However, the geographic spread of DDoS attacks is widening. Notably, France is almost on par with India, experiencing 8.4% of the attacks. The UK is also seeing a significant share, with 8.2% of the attacks occurring there.
The United Arab Emirates faced 7.6% of the global DDoS attacks, a notably high figure for the country. Russia and Ukraine also saw substantial shares, with 7.3% and 4.6% respectively. The majority of these incidents in Russia and Ukraine are linked to hacktivism, stemming from the ongoing conflict between the two nations.
The Israel-Palestine conflict has indeed influenced cyber activities in the MENA region, particularly Israel, where 4.2% of attacks took place. We have observed increased attacks by pro-Hamas hacking groups such as Cyber Av3ngers and Ghosts of Palestine. Additionally, there’s notable activity from groups like Anonymous Sudan and the pro-Russian group Killnet.
DDoS Attacks in 2023: breakdown by protocol
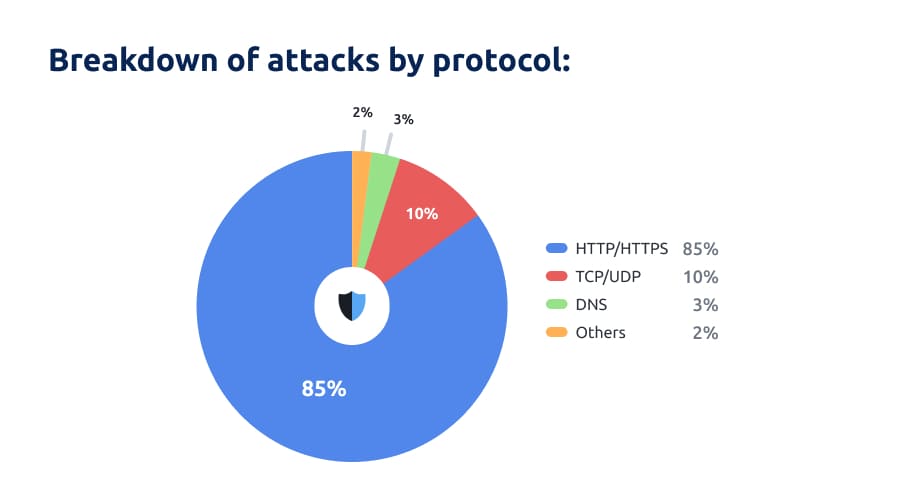
Analyzing the year as a whole, 86% of attacks targeted the HTTP/HTTPS protocols, significantly outpacing other methods. This dominance aligns with the trend for widespread use of mixed and cloud-based botnets. TCP/UDP attacks accounted for 10% of the total, while DNS attacks comprised 3%. Although DNS attacks constituted a smaller overall share, they saw significant growth, particularly in the third and fourth quarters of the year.
Given the hierarchical structure of DNS, an attack on a higher-level server can have a cascading effect, impacting a broader range of services. Threat actors frequently targeted gaming and telecom operators with DNS attacks, as these services heavily rely on DNS resolution for their operation.
Conclusions
As we conclude our analysis of this quarter’s DDoS attack trends, several key factors emerge prominently:
- Geopolitics Driving DDoS Attacks: Geopolitical tensions are a major factor in the surge of DDoS attacks, particularly in countries like the USA, Russia, Ukraine, Israel, Germany, France, Poland, and the UAE.
- Multi-Vector Attacks: We’ve seen 108% increase in multi-vector DDoS attacks, mainly by state-sponsored groups.
- Smokescreening: There’s been a 54% increase in using DDoS for smokescreening to cover other malicious activities like data theft or network breaches.
- The largest DDoS attack in 2023 peaked at 1.4 Tbps. It was equivalent to a small country’s daily internet traffic.
- Evolving Botnets: Botnets, especially those using cloud computing, were involved in 43% of DDoS attacks.
- Expanding Geographical Reach: There was increased DDoS activity in the APAC and MENA regions, with a 45% surge in the MENA region, partly due to Russian companies’ relocation.
This year has marked a noticeable surge in DDoS attack capabilities, with an unprecedented involvement of state-sponsored groups. However, many organizations are still playing catch-up in implementing effective DDoS protection measures.
We’re witnessing a constant tug-of-war between security firms and threat actors. Despite state-sponsored attackers developing increasingly sophisticated tools, advanced DDoS protection solutions like those offered by StormWall are proving to be highly effective.
The real challenge, though, lies in the limited scope of protection currently in place. Our goal with these reports is to heighten awareness about DDoS threats. We aim to inform security professionals about evolving attack vectors and to make business owners more knowledgeable of the risks.
The trend is clear: attack volumes have been rising year after year. This pattern is likely to continue, underscoring the urgent need for widespread adoption of robust security measures.

DDoS Protection for Websites
- Activate protection in 10 minutes
- 24/7 technical support




















