About the report
StormWall — an international provider of DDoS protection services — analyzed the attacks performed against its customers in the third quarter of 2022. The report looks at the situation in the telecommunications, fintech, entertainment, education and logistic industries.
The global outlook
We observed an unprecedented growth in the number of DDoS attacks in 2022. Unfortunately, this trend continued into the third quarter of the year. There were 90% more attacks in Q3 2022 compared to Q3 2021. The telecommunications industry was targeted the most, with entertainment, fintech and ecommerce sectors also suffering heavily.
The duration of attacks is also increasing, in Q3 2022, the average duration of an attack was 60% longer than in Q3 2021.
We attribute the growth to unusually high activity of organized hacktivists. Additionally, we’ve seen a recent emergence of new open source tools, which are now being adopted by hackers. New tools not only enabled threat actors to launch prolonged floods, lasting up to multiple days, but also allowed them to perform more powerful attacks than ever before. Some of the application layer floods we observed exceeded 700,000 packets per second. The most powerful one we recorded in Q3 2022 topped at 763 Gigabytes per second (Gbps).
It is noteworthy, that by the end of the Q3 2022 hackers became less active than they were at the start of the quarter. However, even if this slow-down continues into the fourth quarter of the year, it is likely temporary. There is little reason to believe that the growing trend in the number of attacks will reverse in 2023.
DDoS attack statistics by industry
Telecommunication
The largest share of attacks (43.2%) in Q3 2022 took place in the telecom industry. The number of attacks in this sector grew by 7 times since Q3 2021.
(Note that hosting service providers and cloud services make up 40% of the telecom industry in our classification).
Most of the attacks on telecom were carried out with the aim of extortion and blackmail. Such a high activity in the sector can be attributed to two reasons. One: as more and more companies shifted to distributed workflows during the pandemic, many vital business processes started revolving around data networks and online communication. This created a perfect opportunity for ransom, which couldn’t go unnoticed by hackers. And two: in Q3 2022 politically motivated hacktivists very actively targeting telecom organizations in Russia.
Entertainment
Entertainment was the second most attacked sector (21.3% share). The number of attacks grew by 18 times since Q3 2021, which is the fastest rate we observed.
It is noteworthy that despite a fast increase of attack numbers, the overall share of attacks in this sector is continuing to decrease. We attribute this to two reasons: firstly, the quarantine measures around the world are being lifted. People are spending more time outside and less time consuming online content. This makes the entertainment industry less lucrative for hackers. Secondly, the shares of other sectors comparatively increased due to a high activity of hacktivists, who are less focused on targeting entertainment companies.
Fintech
The third most affected sector is Fintech, where we recorded 16,3% of attacks. The number of attacks increased by 9 times since Q3 2021.
Government-owned banks often became targeted by politically motivated hacktivists. Culprits formed organized groups sometimes counting several hundred thousand and targeted banks and payment providers. Many of the attacks were directed at Russian companies, including government and privately owned banks.
E-commerce
The fourth largest share was observed in the e-commerce industry, with 14,8% of attacks recorded in Q3 2022. The number of attacks increased by 7 times since Q3 2021.
The main goal of DDoS actors targeting this sector remains extortion and blackmail. Consumer intent to shop online continues to increase — even post Covid, most shoppers make more online orders than before. This means that the industry will continue to attract the attention of hackers. Also, attacks are sometimes carried out by competitors to increase market share.
Online electronics stores were targeted the most, attracting 53% of attacks on this sector. This is followed by online furniture stores, with a 26% attack share, then apparel stores with 12%, stationery stores with 7%, and others with 2%.
Education
In the education sector, (its share is 2,1%), we observed a 6 times increase in attacks compared to Q3 2021.
While its share remains almost the same, this is one of the fastest growing sectors in terms of the number of incidents. Many of the new attacks were performed by politically motivated hacktivists aiming to disrupt online learning.
Logistics
In logistics (1.3% share), we observed a 30% increase in the number of attacks since Q3 2021. Most of the attacks were observed in Russia, where supply chains were targeted by hacktivists to create delays.
DDoS attacks by protocols
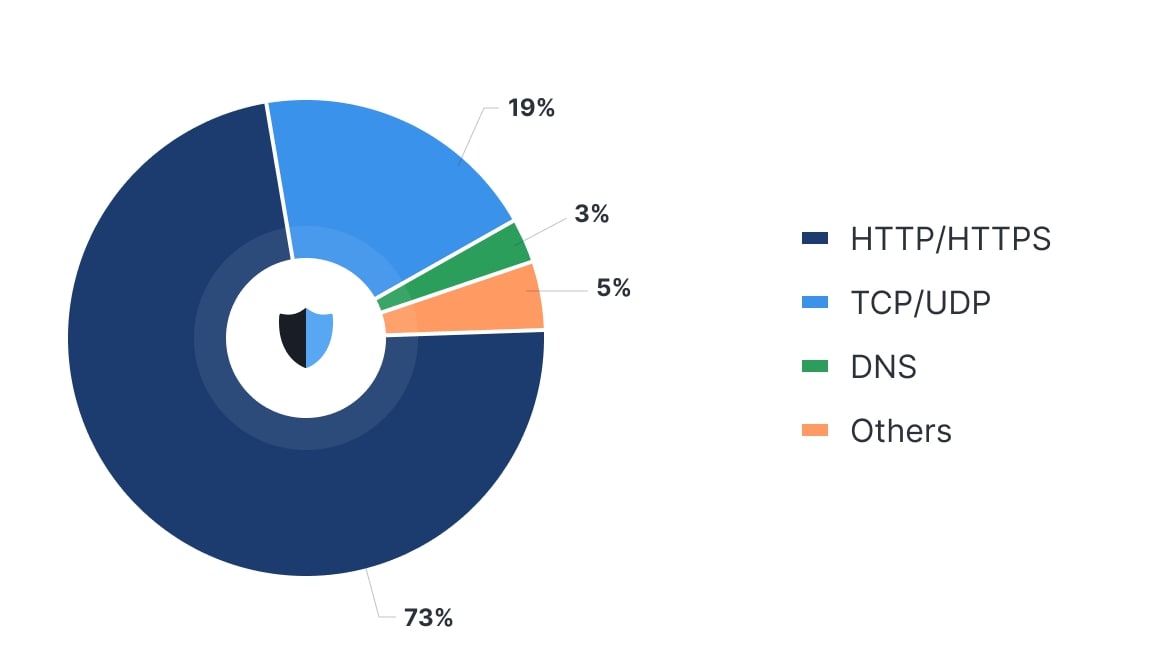
The majority of attacks in Q3 2022 (73%) targeted the application layer of the OSI model. Fewer (19%) attacks were carried out on the network and transportation layers and DNC (3%).
The trend completely reversed from 2021. Last year we were observing a steady quarter over quarter increase in the number of packet floods. In Q3 2021, 83% of attacks targeted TCP/UDP protocols and 16% were attacks on the application layer. Naturally, companies implemented security measures. As more targets became resistant to packet floods, hackers changed strategy and started utilizing application layer attacks instead. Also, in 2022, hacktivist groups developed new DDoS tools as part of a campaign against Russian companies and government agencies. In doing so, they made application layer attacks less costly and significantly easier to launch. Hackers quickly took advantage, and began utilizing the new toolsets in attacks on other countries.
General trends and recommendations
The growth rate of DDoS attacks slowed down towards the end of the third quarter of 2022, and this might seem like a big win. However, it is important to remember that we’re still in the record-breaking year. If we look at the bigger picture, the overall trend is worrying.
In 2022, hacktivists, have developed new tools that enable prolonged, powerful attacks. Until Q3 2022, they were mostly used in politically motivated actions. Recently, threat actors have adopted them and we are going to see more destructive ransom and blackmail attacks targeting all industries.
By analyzing the data collected from our clients, we can forecast that upcoming attacks will exceed 1,000,000 requests per second and have a duration of up to multiple days. To put it another way, in the past even giants like Amazon would rarely face threats of this level. Putting together all these resources against a medium sized business just wasn’t cost effective for threat actors. We believe that the recent evolution of DDoS toolset is going to change that.
This is why we advise companies to acquire professional DDoS protection capable to defend against this upcoming threat.




















