DDoS Protection for Networks
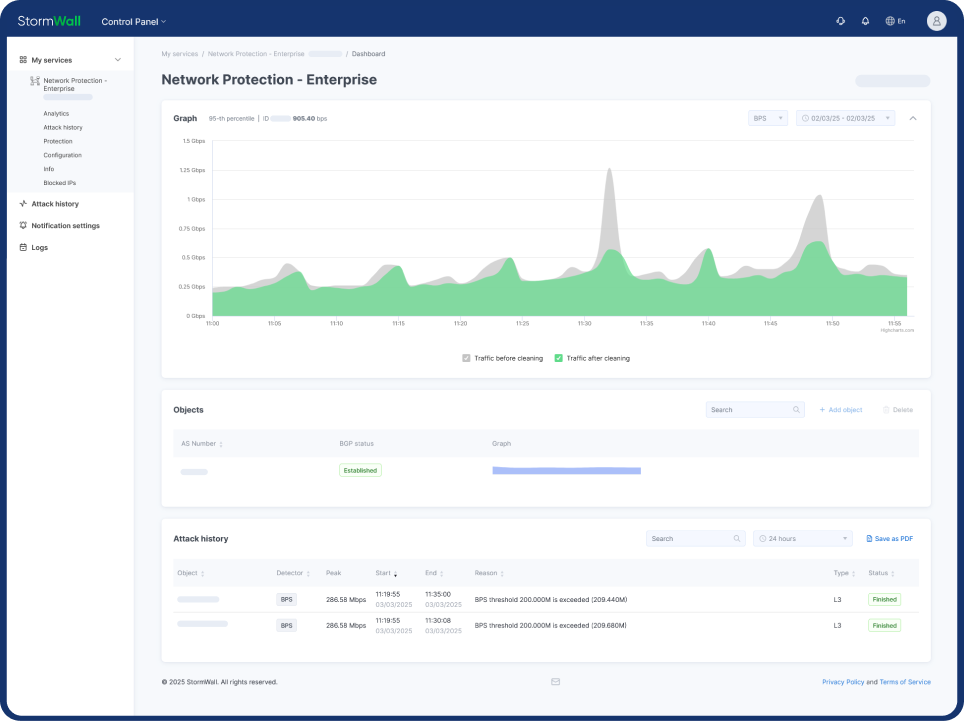
StormWall for Networks
and infrastructure performance
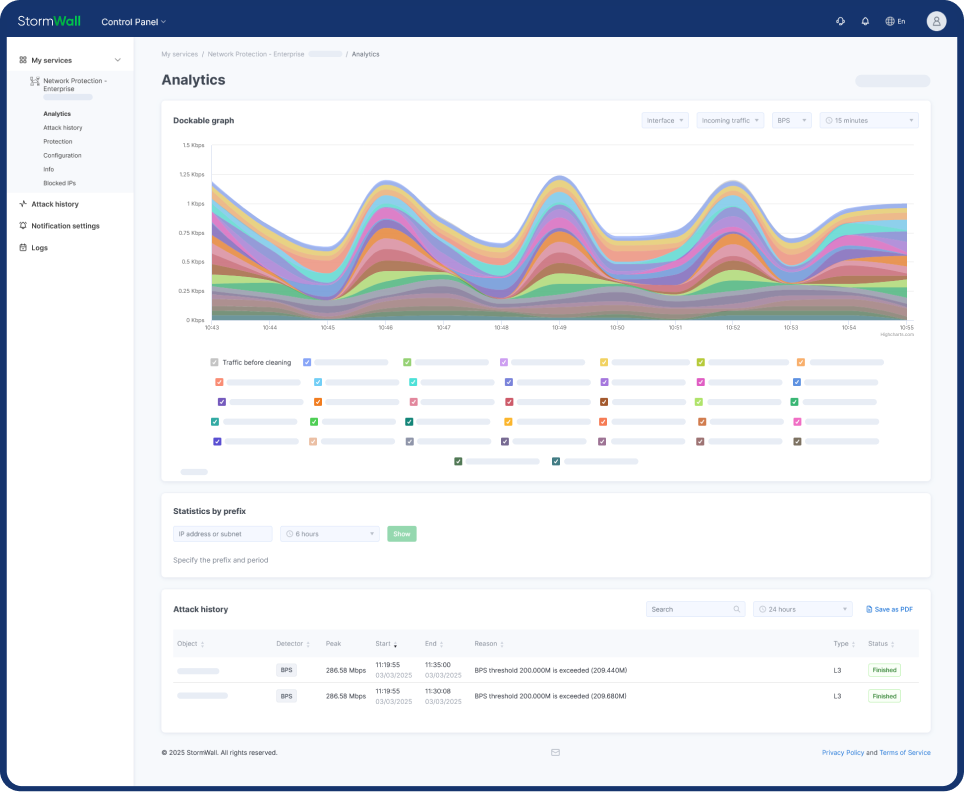
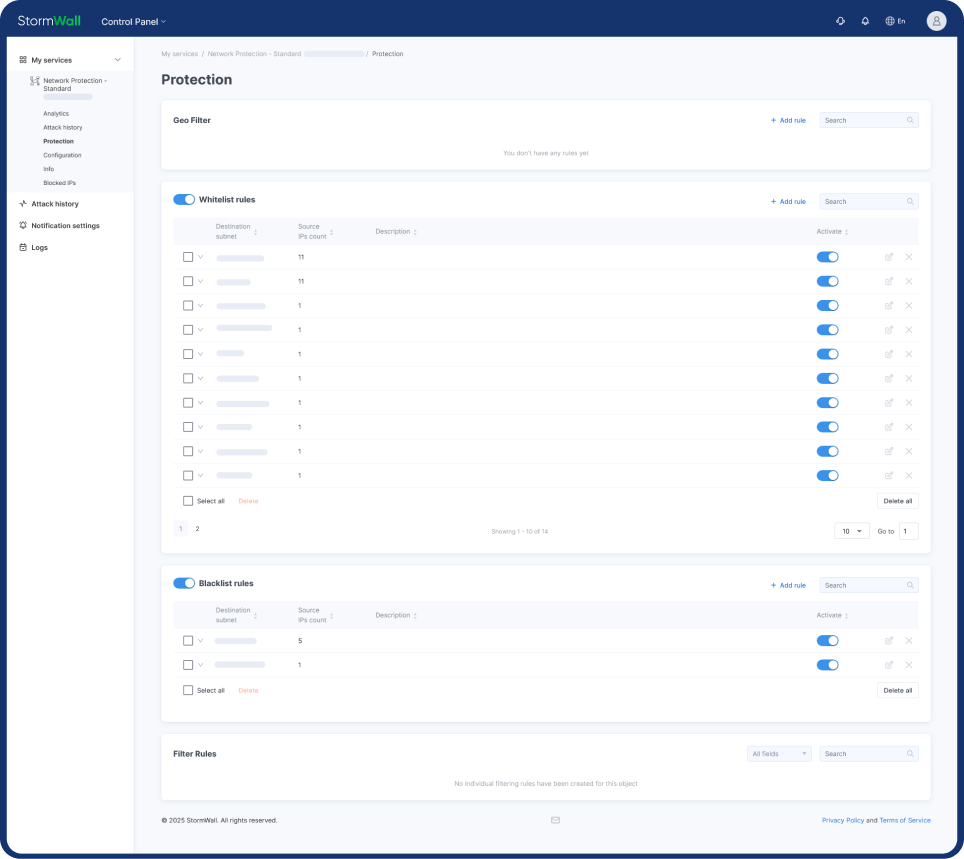
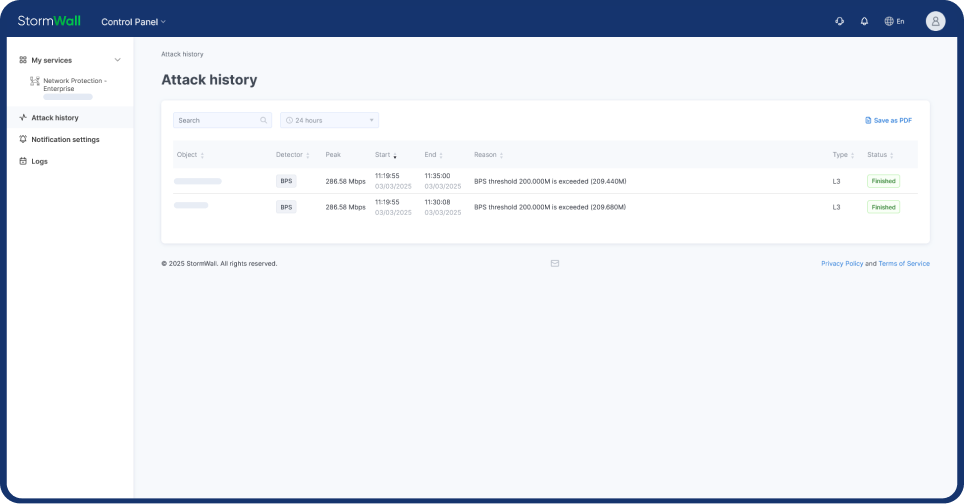
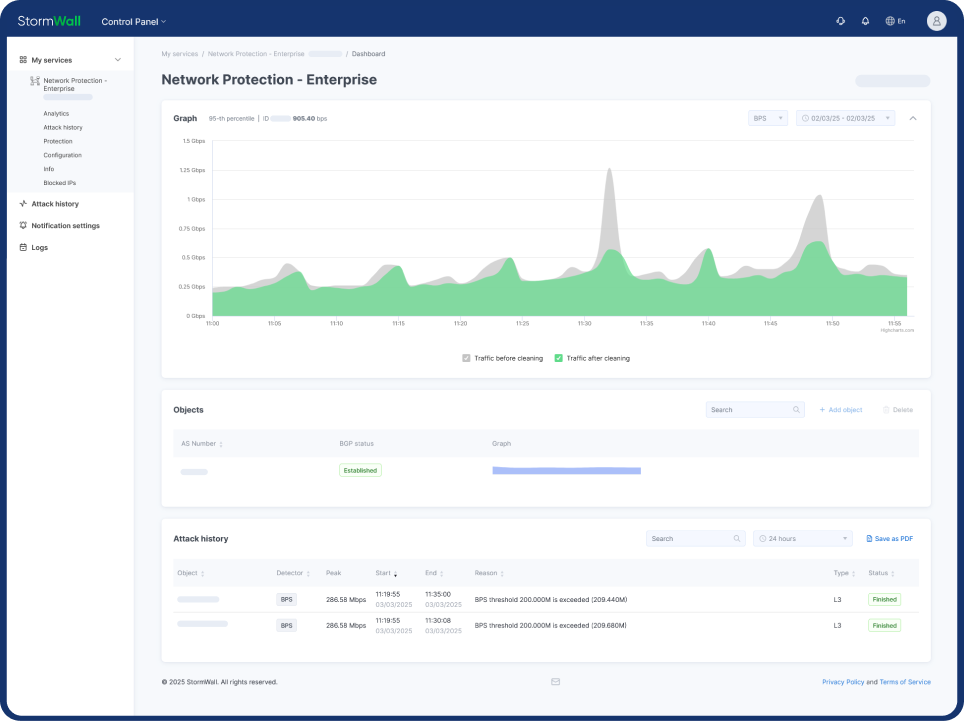
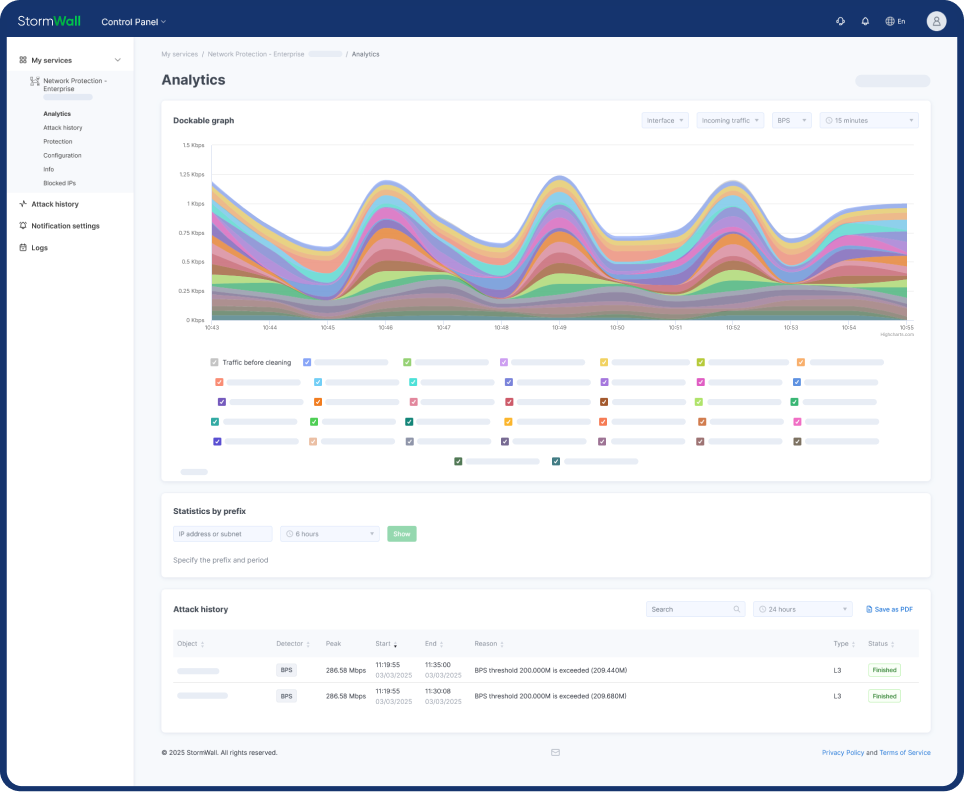
Client Portal













StormWall for Web
WAF and DDoS protection for web applications

StormWall for Networks
DDoS protection for networks via BGP

StormWall for Servers
DDoS protection for TCP/UDP services

Antibot
Reliable protection of web applications from bots

Enterprise-Grade WAF
Protecting web applications with a cloud‑based security tool
For ISP/Telecom
Reliable operation of the network and critical services
For Online Gaming
Uninterrupted gameplay with minimal latency
For Banks
24/7 availability of payments and transfers
For Online Stores
Maximize sales during peak loads

Blog
Company and industry news, educational articles

White Papers
Downloadable materials to stay ahead of evolving threats

How StormWall Works
Explore how our services can protect infrastructure from any type of attack

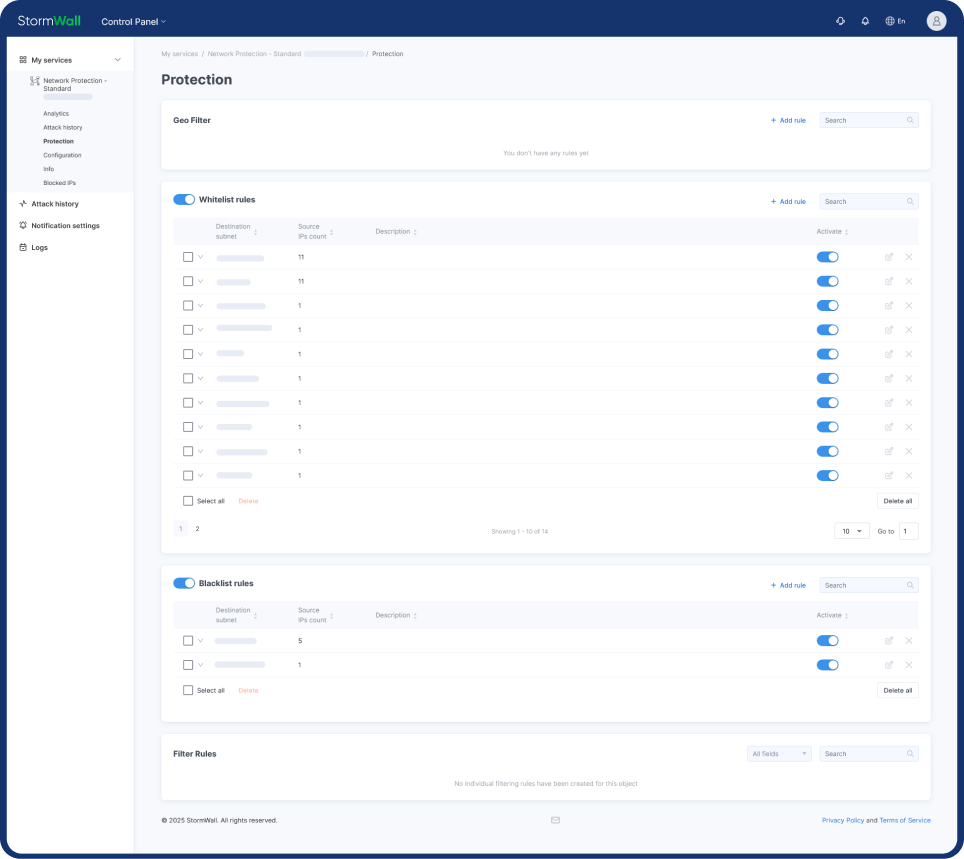
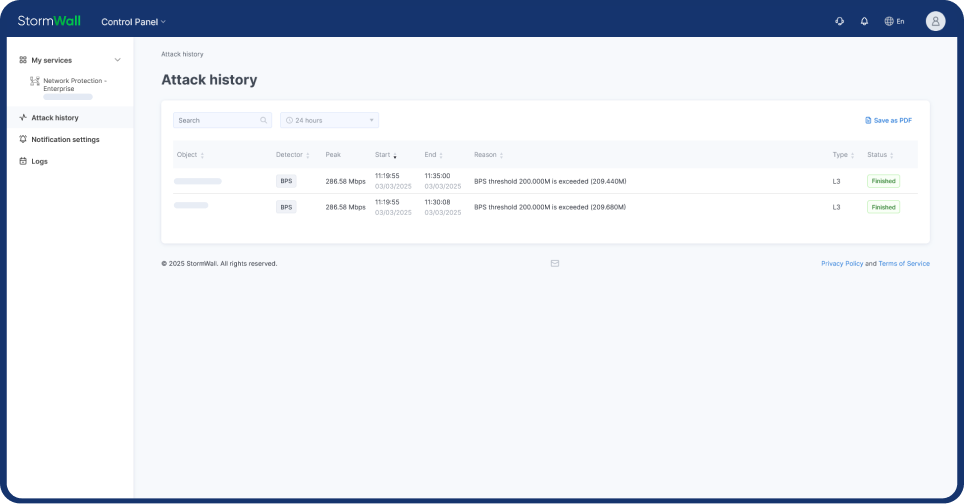
User Guide
Detailed guide on using the Client Portal

Success Stories
Articles with customer case studies

Technology
How StormWall DDoS protection works

API
Automate management of StormWall DDoS protection

Knowledge Base
Cybersecurity terms and definitions

StormWall Partner Program
For resellers and service providers

White Label
Use StormWall DDoS protection under your brand

Affiliates
Attract clients to protect sites from DDoS - and increase your income

About StormWall
Learn more about our company, see contact details and terms of service

Our Clients
Companies protected by us over the years

Media
Articles featuring our company

Why StormWall
Our benefits